Receiving a call from an unfamiliar phone number is a universal experience in the modern digital age. With the exponential rise in automated dialers and telemarketing systems, the average mobile phone user frequently encounters incoming calls bearing no caller identification. The immediate reaction is often a mix of curiosity and hesitation. Deciding whether to answer, ignore, or investigate the number involves understanding the infrastructure of mobile communications and the digital footprints left by telephone numbers.
While the era of the printed, public telephone directory is largely over, the internet and interconnected mobile ecosystems provide alternative methods for identifying the source of a phone call. Finding the owner of a cell phone number for free requires a methodical approach, utilizing public indexing, social media algorithms, and, when necessary, official channels.
This guide explores the mechanics of phone number identification, the limitations of public data, and the specific, cost-free methods available to determine who is behind an unknown number.
The Reality of Phone Number Ownership Data
Before attempting to identify a caller, it is crucial to understand how telecommunications data is categorized and protected. The ease with with a number can be traced depends entirely on how that number is used and the privacy settings of the owner.
Public vs. Private Directories
Historically, landline telephone numbers were automatically indexed in massive public databases, printed annually, and distributed to every household. Cell phone numbers, however, were excluded from these public registries from the very beginning of mobile adoption. Mobile carriers treat subscriber information as proprietary and confidential.
Consequently, there is no master, publicly accessible database of cell phone numbers. If a mobile number remains strictly for personal use and the owner has maintained strict digital hygiene, identifying the owner through free public searches is highly improbable.
The Digital Footprint
A cell phone number becomes identifiable when it bridges the gap between private telecommunications and the public internet. This occurs when a user associates their mobile number with a public profile, a business registration, an online classified advertisement, or a social media account. The larger the digital footprint associated with a specific sequence of digits, the easier it is to perform a successful lookup.
Method 1: Utilizing Search Engine Indexing
The most straightforward, rapid, and accurate method for identifying an unknown number relies on search engine indexing. Search engines constantly crawl the internet, indexing text from billions of webpages, including business directories, public forums, and government databases.
Identifying Business and Commercial Entities
When a business registers a phone number, it typically publishes that number on its official website, social media pages, and local directory listings to attract customers. If the unknown caller is a legitimate business, a search engine query will almost instantly reveal the company’s identity, location, and operating hours.
Tracking Scam and Spam Numbers
Search engines are equally effective at identifying known scammers and automated robocall operations. When hundreds of individuals receive calls from the same disruptive number, they frequently report the digits on community complaint boards and consumer protection websites. Searching the number will often yield results from these forums, confirming the number’s status as a known nuisance.
Advanced Search Techniques
To maximize the effectiveness of a search engine lookup, utilize specific search operators:
-
Exact Match Formatting: Enter the phone number in quotation marks (e.g., “555-0198”) to force the search engine to look for that exact sequence of numbers, reducing irrelevant results.
-
Alternative Formatting: Try various standard formats, as different websites format numbers differently. Search for (555) 000-0198, 555-000-0198, and 5550000198.
Method 2: Social Media and Messaging App Synchronization
Modern social networking and instant messaging applications rely heavily on phone numbers for account verification, security, and network building. By exploiting the contact synchronization features built into these platforms, you can often identify a caller.
The Mechanics of Contact Syncing
When you install an application like WhatsApp or Facebook, the software requests permission to access your device’s local contact list. The application then uploads these phone numbers to its servers and cross-references them against its user database. If a number in your phonebook matches a registered user, the application suggests that person as a connection.
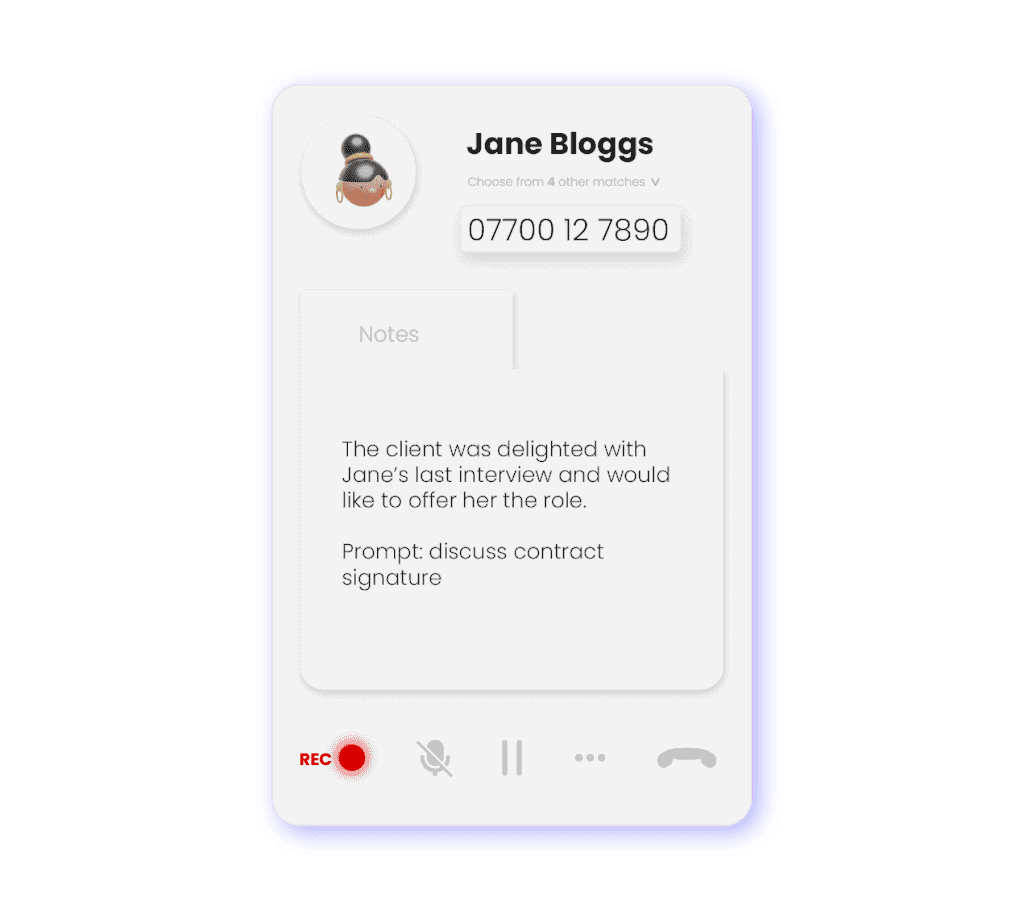
Step-by-Step Identification via Messaging Apps
To use this method, you must temporarily save the unknown number to your device’s contacts.
-
Open your phone’s dialer or call log.
-
Select the unknown number and choose the option to “Create New Contact.” Save it with a placeholder name, such as “Unknown Caller.”
-
Open a messaging platform, such as the WhatsApp Messenger on Google Play.
-
Navigate to the “New Chat” or “Contacts” section within the application.
-
Search for the placeholder name you created.
-
If the owner of the number has registered an account with that application, their profile will appear. This profile often includes a display name, a profile picture, and a status update, providing clear clues to their identity.
Identification via Social Networks
Social media platforms use a similar algorithmic approach to suggest “People You May Know.”
-
Ensure the unknown number is saved in your device’s address book.
-
Open a social media application, such as Facebook on the App Store.
-
Navigate to the “Friends” or “Discover People” section.
-
Allow the application to sync your device contacts.
-
Review the suggested profiles. The algorithm will prioritize accounts linked to the phone numbers in your address book. If a new, unfamiliar profile appears in your recommendations immediately after saving the number, it is highly probable that the profile belongs to the caller.
Note: The success of this method depends entirely on the user’s privacy settings. If the owner has configured their account to prevent individuals from searching for them via their phone number, no profile will appear.
Method 3: Involving Law Enforcement
While search engines and social networks are useful for satisfying curiosity or identifying telemarketers, they are insufficient when dealing with malicious communications. In situations involving continuous harassment, explicit threats, or targeted extortion, identifying the caller becomes a matter of public safety.
When to Escalate to Authorities
Law enforcement agencies possess the jurisdiction and technological resources to bypass telecommunications privacy barriers. You should contact the police if you receive calls that include:
-
Threats of physical harm or violence.
-
Persistent, targeted stalking or harassment.
-
Attempts at financial extortion or severe fraud.
The Investigative Process
Police departments do not use public search engines to trace numbers. Instead, they utilize established legal procedures. When a formal report is filed, detectives can issue a subpoena or a warrant directly to the telecommunications carrier holding the number.
The carrier is legally obligated to provide the subscriber’s exact name, billing address, account history, and potentially the physical location data of the mobile device. This process is highly regulated and requires a demonstrably valid legal reason; authorities will not unmask a caller simply to satisfy personal curiosity.
The Limitations of Online “Free” Lookup Tools
A simple web search for “phone number lookup” will yield thousands of websites claiming to offer instant, free identification of any cell phone number. Understanding the underlying business model of these platforms is crucial for managing expectations and protecting your own data.
Data Brokers and Aggregation
These websites are operated by data brokers. They function by scraping public records, purchasing marketing databases, and aggregating information from various online sources. When you enter a number, the site queries its internal database for a match.
The Illusion of “Free” Services
The vast majority of these platforms are not truly free. They operate on a freemium model designed to bait users. The initial search will typically return vague information—such as the geographic region (city and state) associated with the area code, and the original carrier the number was registered to.
To view the actual name or address of the owner, the website will prompt you to purchase a subscription, pay a one-time fee, or enter your credit card information for a “trial.”
Inaccuracy and Outdated Records
Even if a user chooses to pay for a report, the data is frequently inaccurate. Mobile numbers change hands regularly. When a person cancels their cellular service, the carrier places the number in a holding pool before reassigning it to a new customer. Data broker websites rarely update their databases quickly enough to reflect these changes, often providing the name of the previous owner rather than the current one.
Privacy and Security Concerns
Interacting with unverified lookup platforms carries significant digital risks. Some sites require users to create an account and upload their own contact lists to gain access to the database, thereby sacrificing the privacy of everyone in their address book. Others are heavily monetized through aggressive advertising networks that may expose the user’s device to tracking cookies or malicious software.
Device-Level Defenses: Blocking Unknown Callers
If identifying the caller proves impossible or unnecessary, the most effective strategy is to eliminate the disturbance entirely. Modern mobile operating systems feature robust, built-in tools designed to filter out communication from numbers not saved in your personal contacts.
iOS Configuration
Apple’s iOS includes a native feature specifically engineered to handle unwanted calls without requiring the installation of any extra applications.
-
Open the “Settings” application on the home screen.
-
Scroll down and select the “Phone” menu.
-
Locate the option labeled “Silence Unknown Callers.”
-
Toggle the switch to the ON position.
When activated, any incoming call from a number that is not stored in your Contacts, recent outgoing calls, or Siri Suggestions will be immediately routed to voicemail without the device ringing. The number will still appear silently in your “Recents” list, allowing you to review it later.
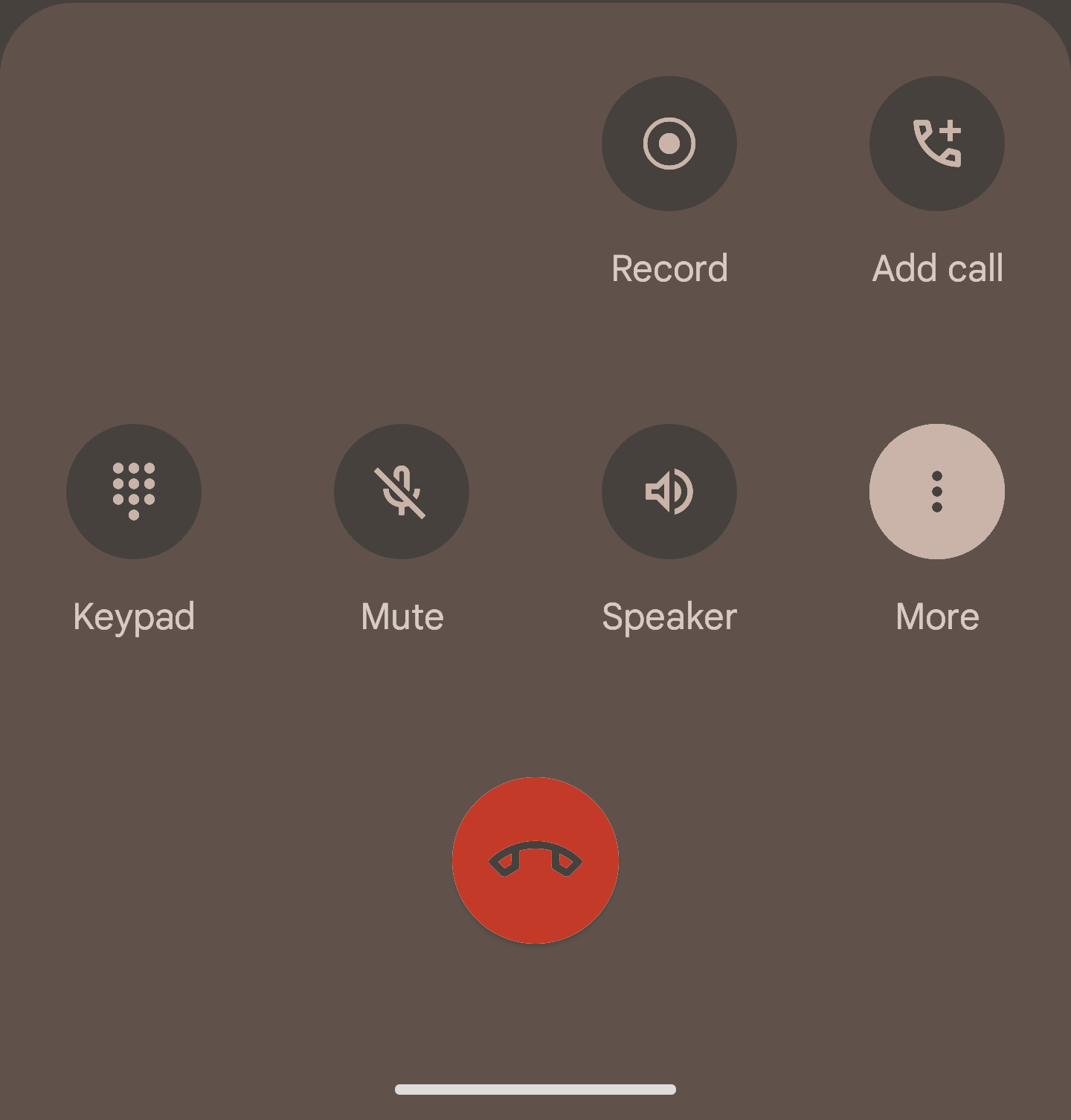
Android Configuration
The Android operating system offers a similar, highly effective method for blocking unrecognizable numbers directly through the native dialer application.
-
Launch the default “Phone” application.
-
Tap the three-dot menu icon, usually located in the top-right corner of the interface.
-
Select “Settings” from the dropdown menu.
-
Navigate to “Blocked numbers” or a similarly named call-blocking section.
-
Toggle the switch for “Block unknown numbers” or “Block calls from unidentified callers.”
Activating this setting ensures that your phone will not ring for numbers hidden by the caller or absent from your address book, providing a seamless, undisturbed mobile experience.
Parental Management and Device Oversight
The volume of unsolicited communication directed at mobile devices presents a unique challenge for parents managing their children’s smartphones. Ensuring that minors do not interact with scammers or inappropriate callers is a primary concern.
Implementing device-level blocks is the first step. Furthermore, integrating a general device management strategy—similar to the organizational tools provided by platforms like FreePhoneSpy—allows for structured oversight of a device’s communication logs. While respecting appropriate boundaries, managing the contact list and reviewing call histories ensures that the communication ecosystem remains secure and restricted strictly to known, approved individuals.
Conclusion
The infrastructure of modern telecommunications is designed to prioritize the privacy of the individual subscriber. Consequently, finding the owner of a cell phone number for free is a process of deduction rather than a simple directory lookup.
By leveraging the massive indexing power of search engines, you can quickly identify businesses, telemarketers, and known scam operations. By understanding the contact synchronization algorithms of major social media and messaging platforms, you can often match a number to a public profile. However, it is essential to recognize the limitations of these methods and the deceptive nature of many online lookup websites. When faced with persistent, threatening, or harassing calls, the only appropriate and effective response is to engage law enforcement, who possess the legal authority to bypass privacy protections. Ultimately, utilizing the built-in call-filtering features of your smartphone remains the most effective way to manage and eliminate the daily annoyance of unknown callers.
Frequently Asked Questions
Why isn’t there a public directory for cell phone numbers like there is for landlines? Cellular networks were developed with different privacy standards than legacy landline systems. Mobile carriers treat subscriber data as proprietary and confidential. Furthermore, because users pay for incoming cellular calls (historically, out of a minute allowance), publishing numbers publicly would subject users to financial burdens from unsolicited calls.
Can I find out who called me if the caller ID says “No Caller ID” or “Restricted”? No. When a call displays as “Restricted” or “No Caller ID,” the caller has intentionally used a network prefix (such as *67) or a device setting to strip their identifying data from the transmission before it reaches your phone. Because the data never arrives at your device, neither search engines nor social media syncs can identify the caller.
Are reverse phone lookup websites accurate? Generally, no. These websites rely on aggregating public records, marketing lists, and outdated directories. Because mobile numbers are frequently reassigned to new users by the carriers, the data held by these brokers is often obsolete, showing the previous owner’s information rather than the current subscriber’s.
Will saving a spam number to check WhatsApp notify the sender? Simply saving a number to your device’s local contacts does not send any notification to the owner of that number. If you open WhatsApp and view their profile picture or status, they are not alerted. However, if you accidentally initiate a chat, call, or interact with their profile on other social media platforms (like ‘liking’ a post), they will be notified.
